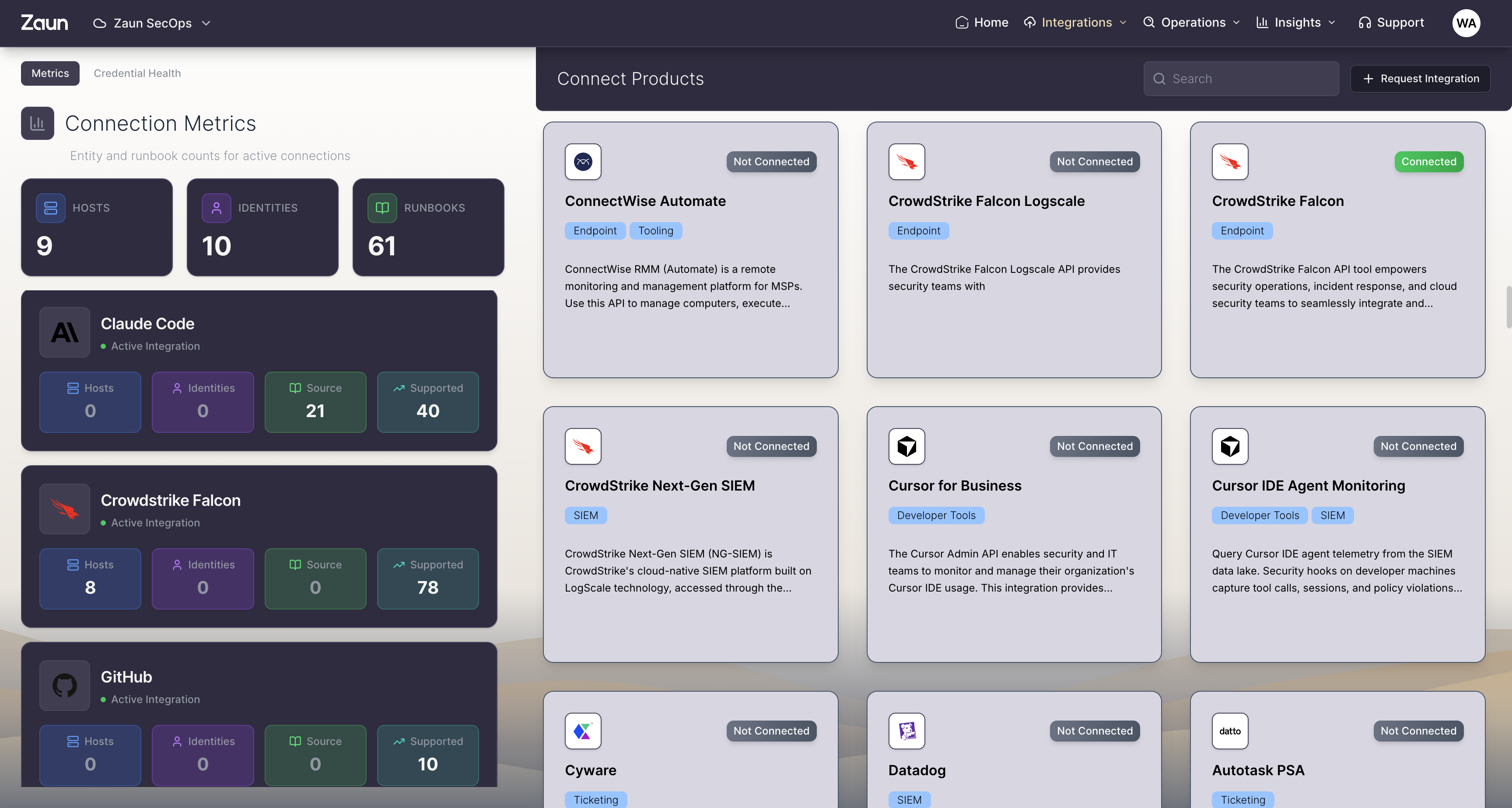
Plug into everything, the day you start.
Zaun connects to 100+ systems by OAuth, API, or sensor. Cloud, identity, endpoint, SaaS, AI providers, and the long tail. No collectors to install, no ingest tax, no waiting. Sources go live in hours and start producing signal the same day.
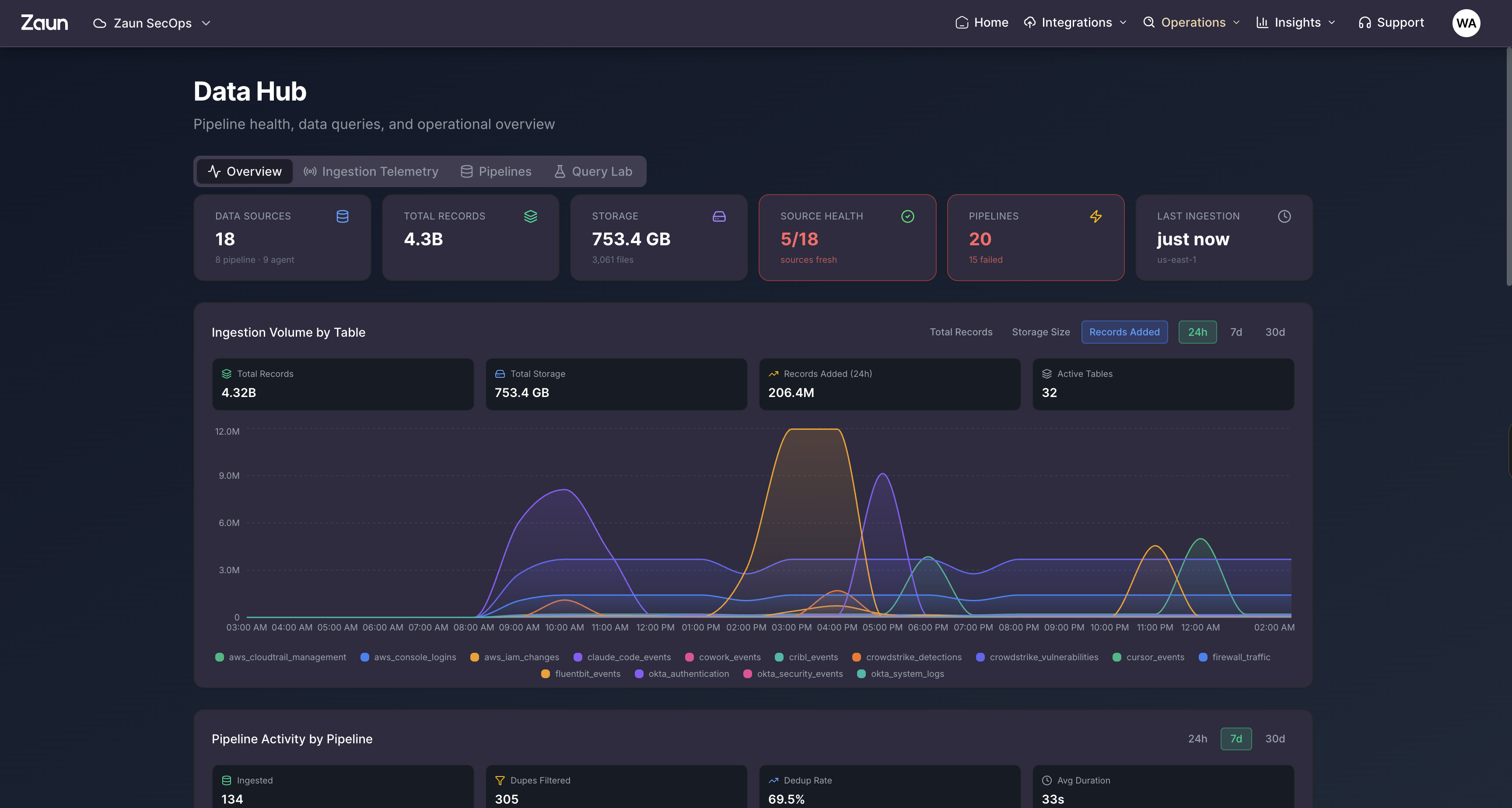
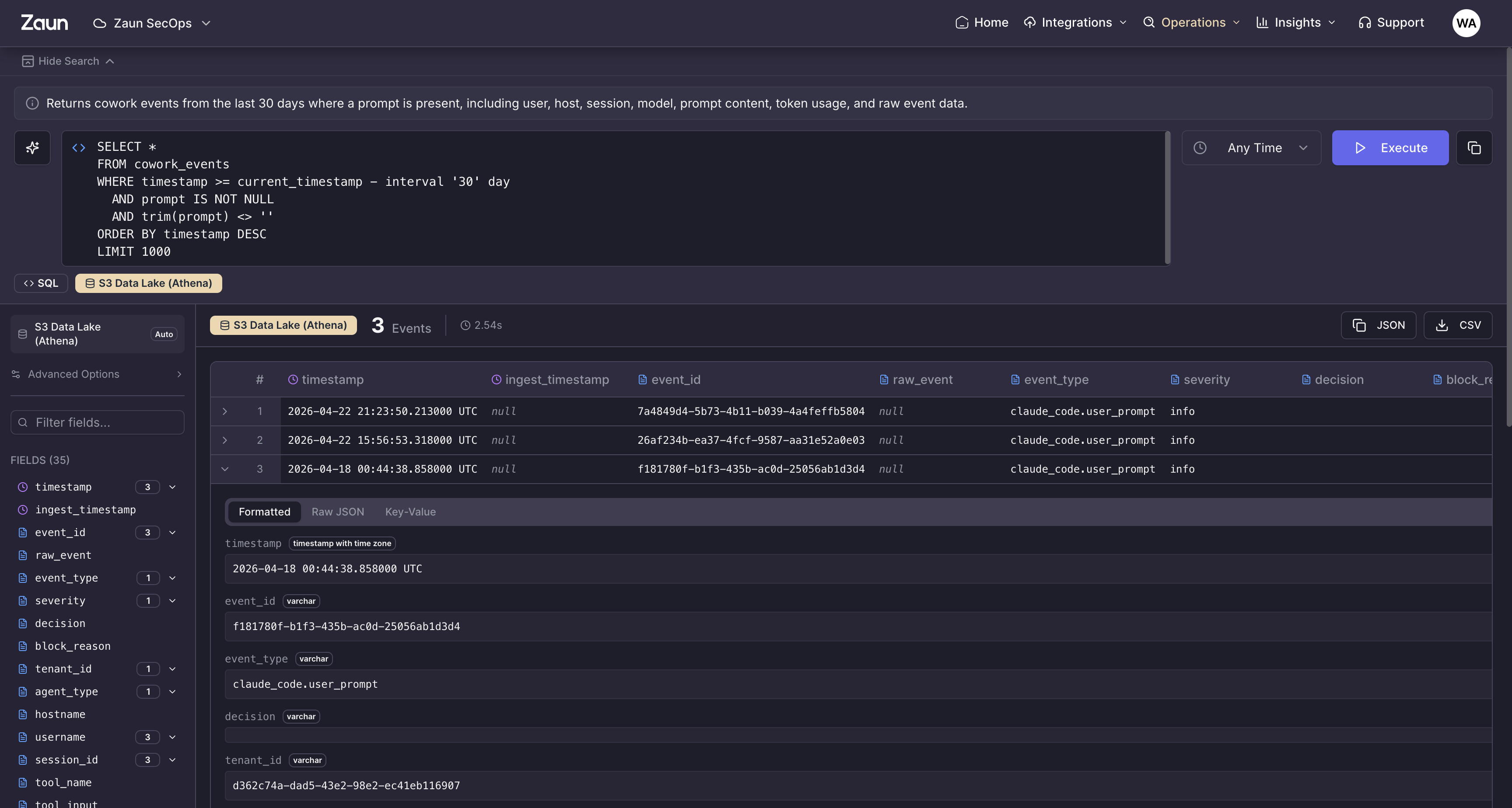
Deep retention. Real hunts.
Zaun Lake keeps only the events that drive compliance, investigations, and threat hunts: authentications, sensitive actions, config changes, network egress, and other events that matter. Tagged and correlated at ingest, hot for as long as you set, and queryable in milliseconds across months of history. Ask in plain English to query the Lake, pivot through investigations, and draft reports without writing a line of SQL. Mappable to NIST 800-171, SOC 2, HIPAA, PCI, and more.
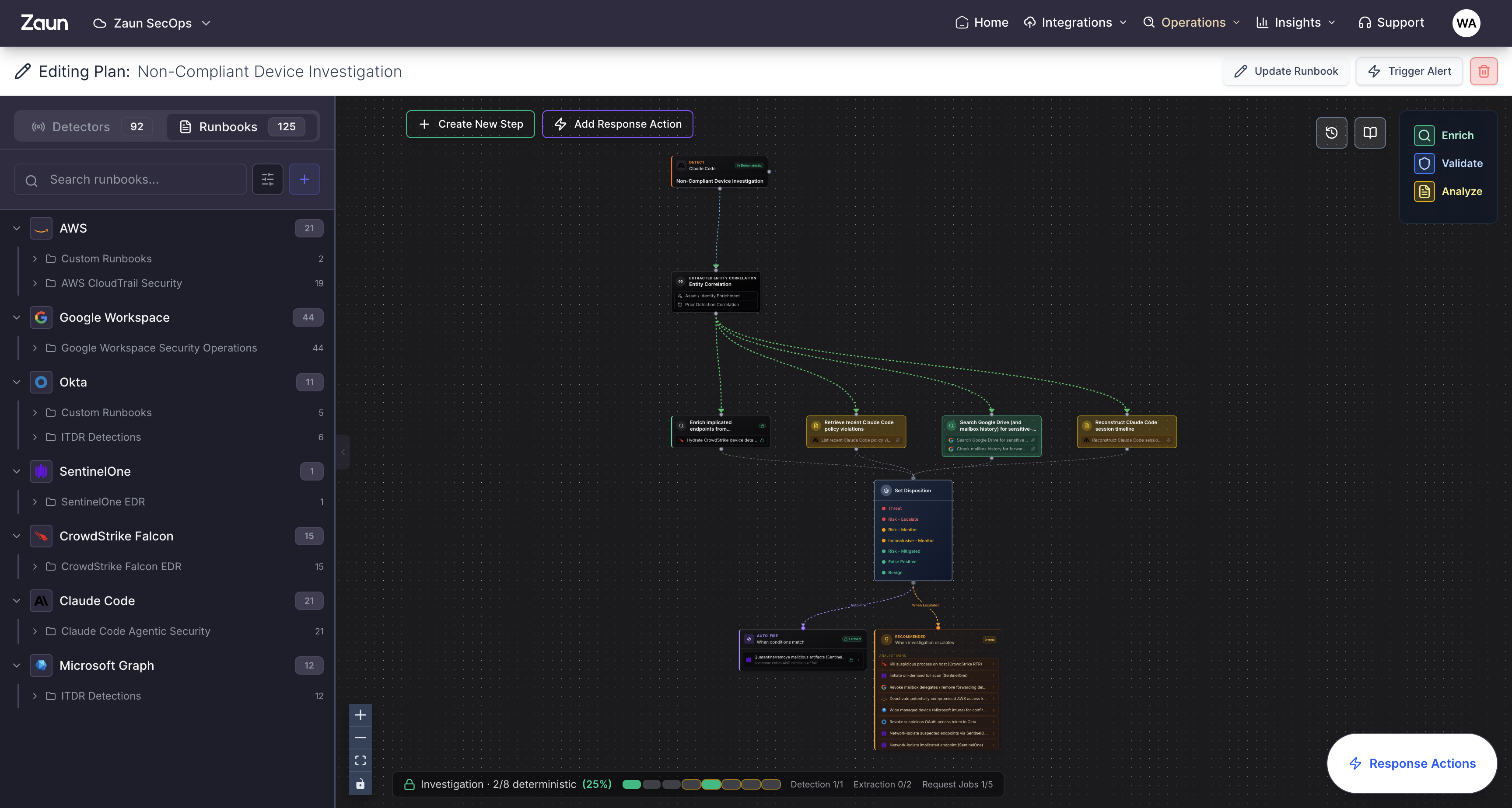
Detections you can read out loud.
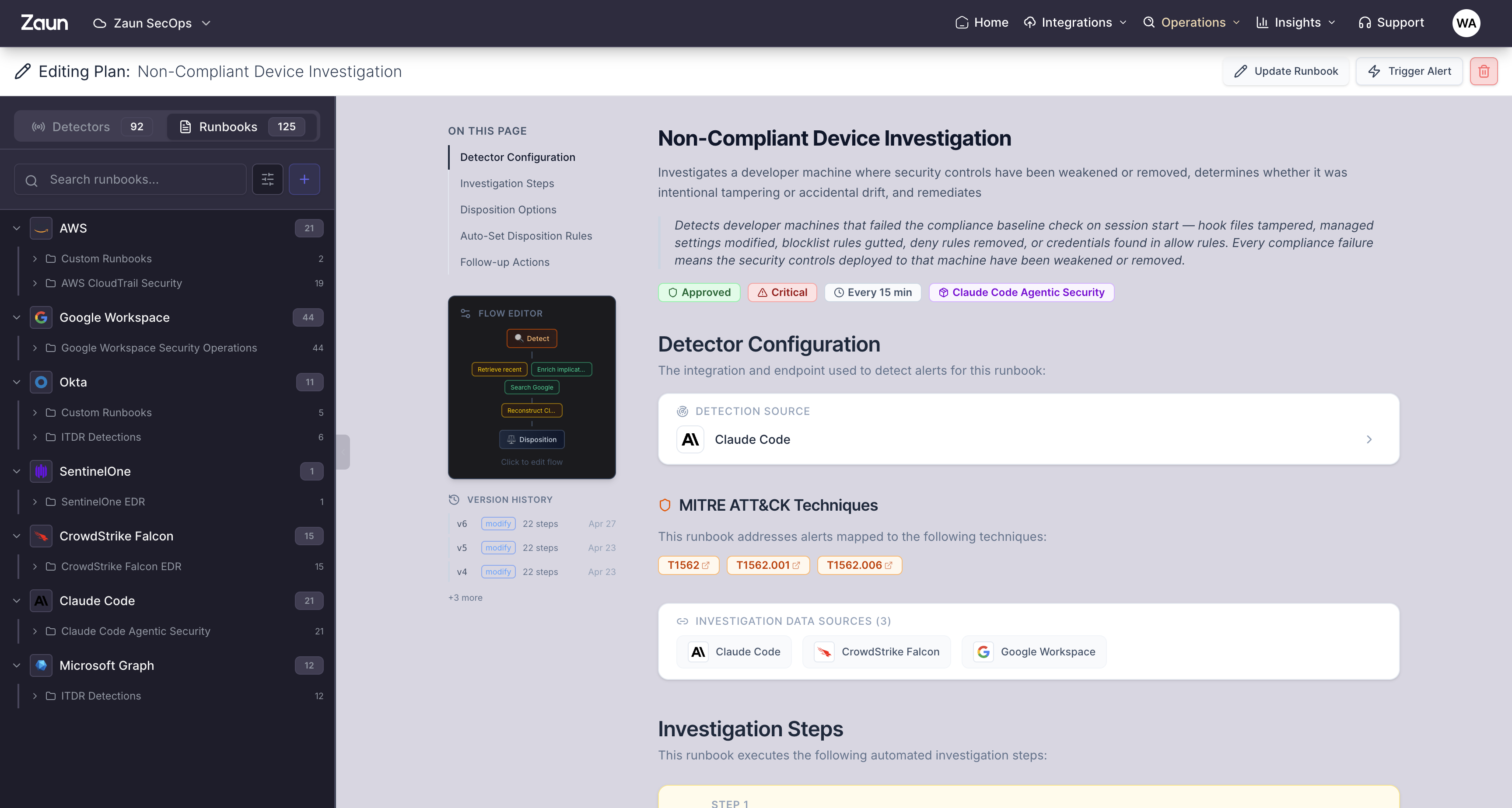
The library is built on MITRE ATT&CK for technique coverage and MITRE D3FEND for the matching defensive countermeasure. Every rule traces back to a technique ID, every runbook step traces back to a documented defense, and the whole thing reads in plain English so anyone on your team can audit, edit, or version-control it. 1,000+ rules across cloud, identity, endpoint, AI, and SaaS, written for your stack. Allow deterministic-only actions to run automatically, while AI recommends to experts.
Plain-English by default
Every rule reads like a sentence. No DSL to learn. Anyone on your team can read, edit, or comment.
Tuned Autonomously
Automatically adapts to your environment and changes based on events, feedback, or weekly tunings.
Versioned and Auditable
Each rule and step is a Zaun artifact, version-controlled, and observable end to end.
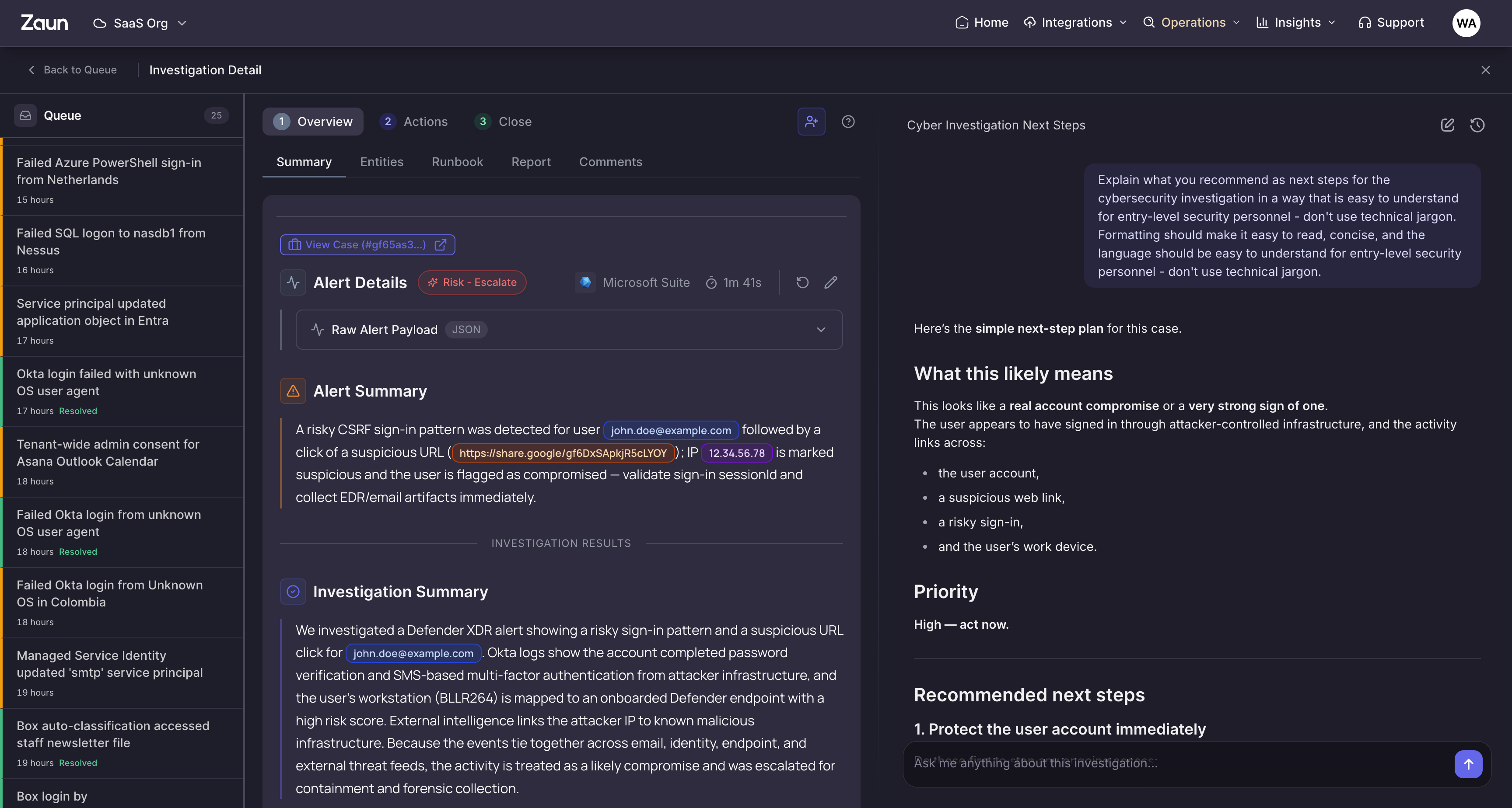
Investigations that show their work.
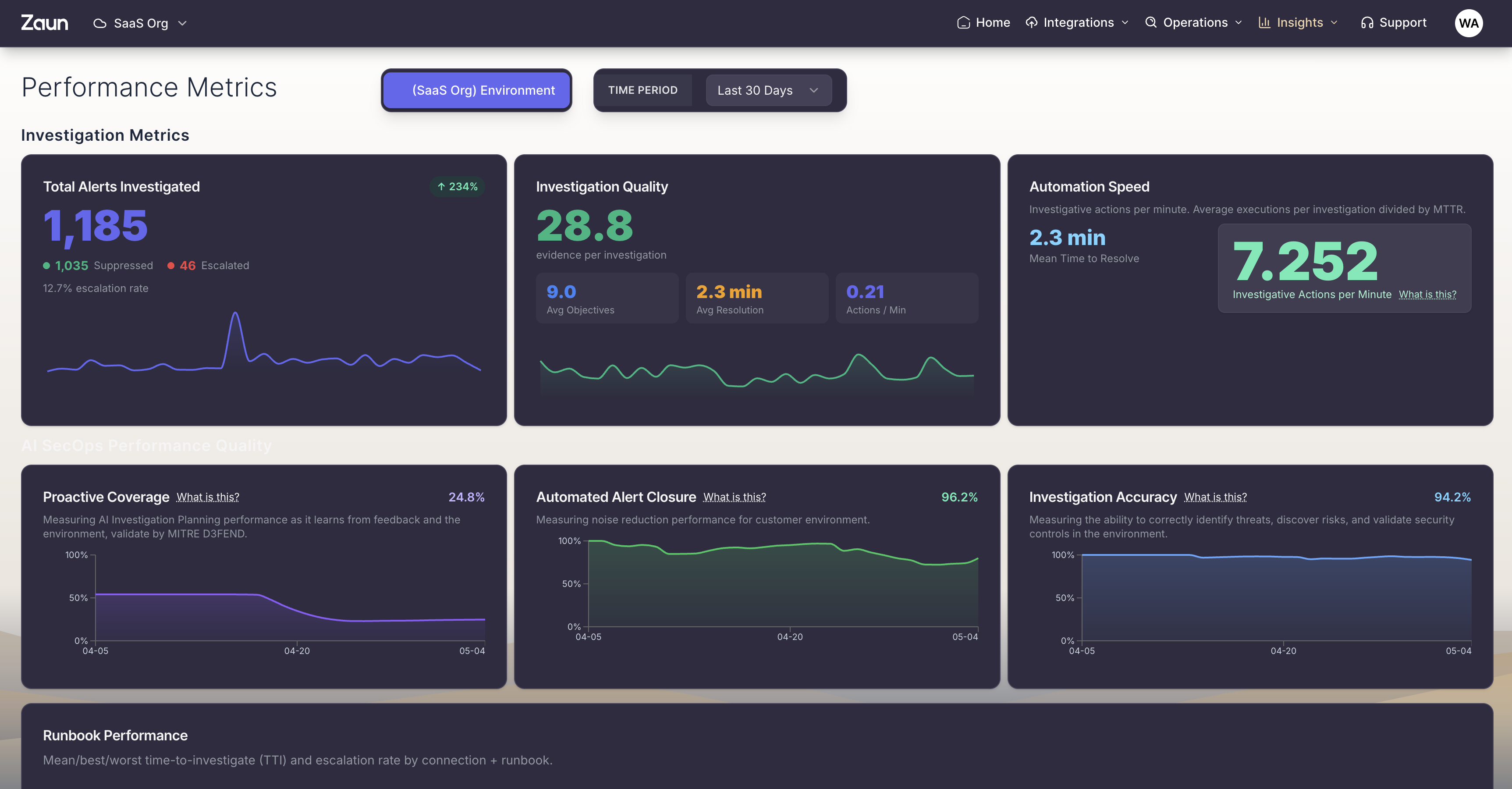
When a detection fires, Zaun closes most investigations in under a minute: pulls evidence from every connected source, correlates the timeline, scores the verdict, and writes a plain-English narrative your team can audit. Humans approve only what matters; the machine handles the grunt work.
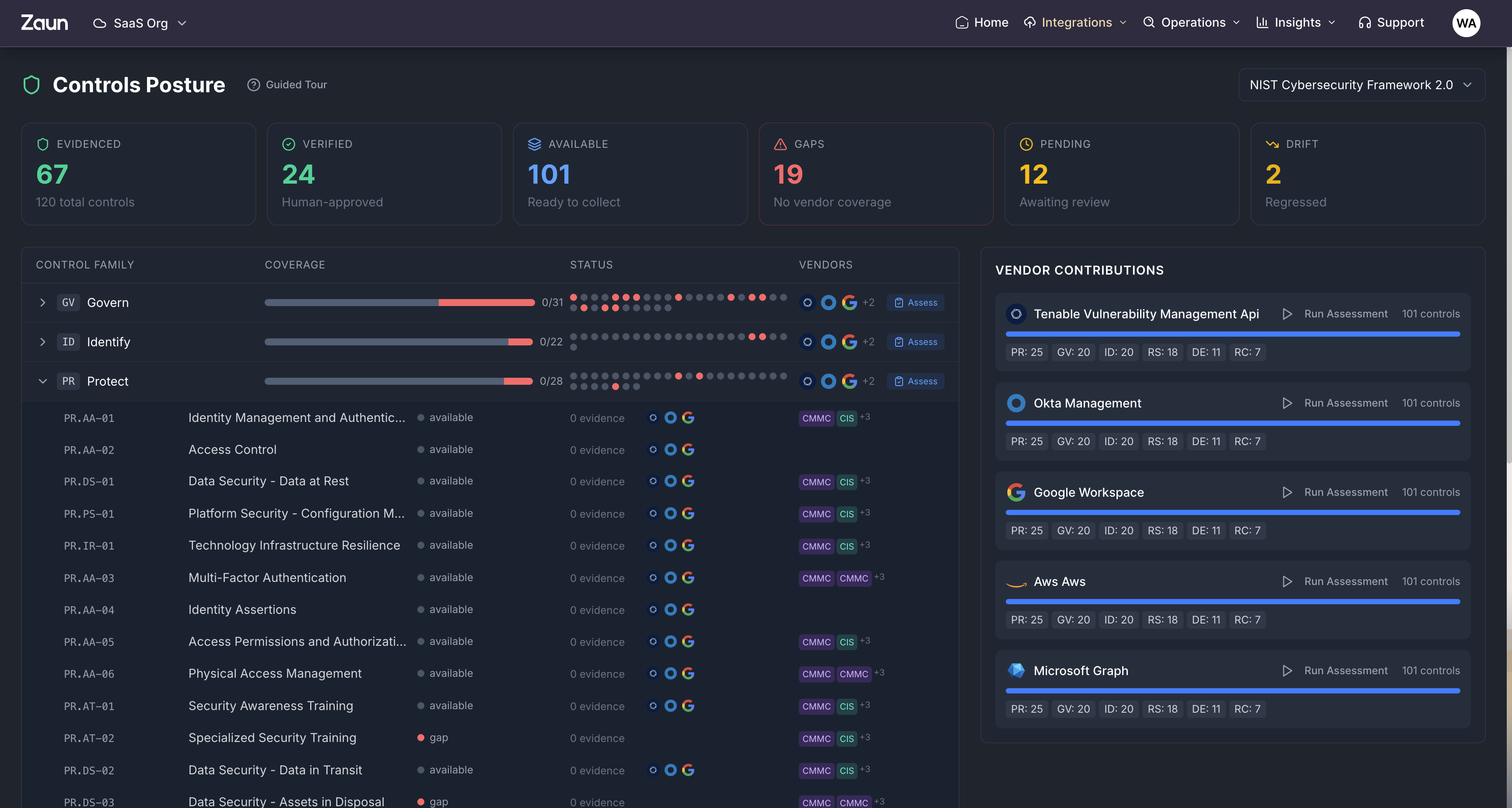
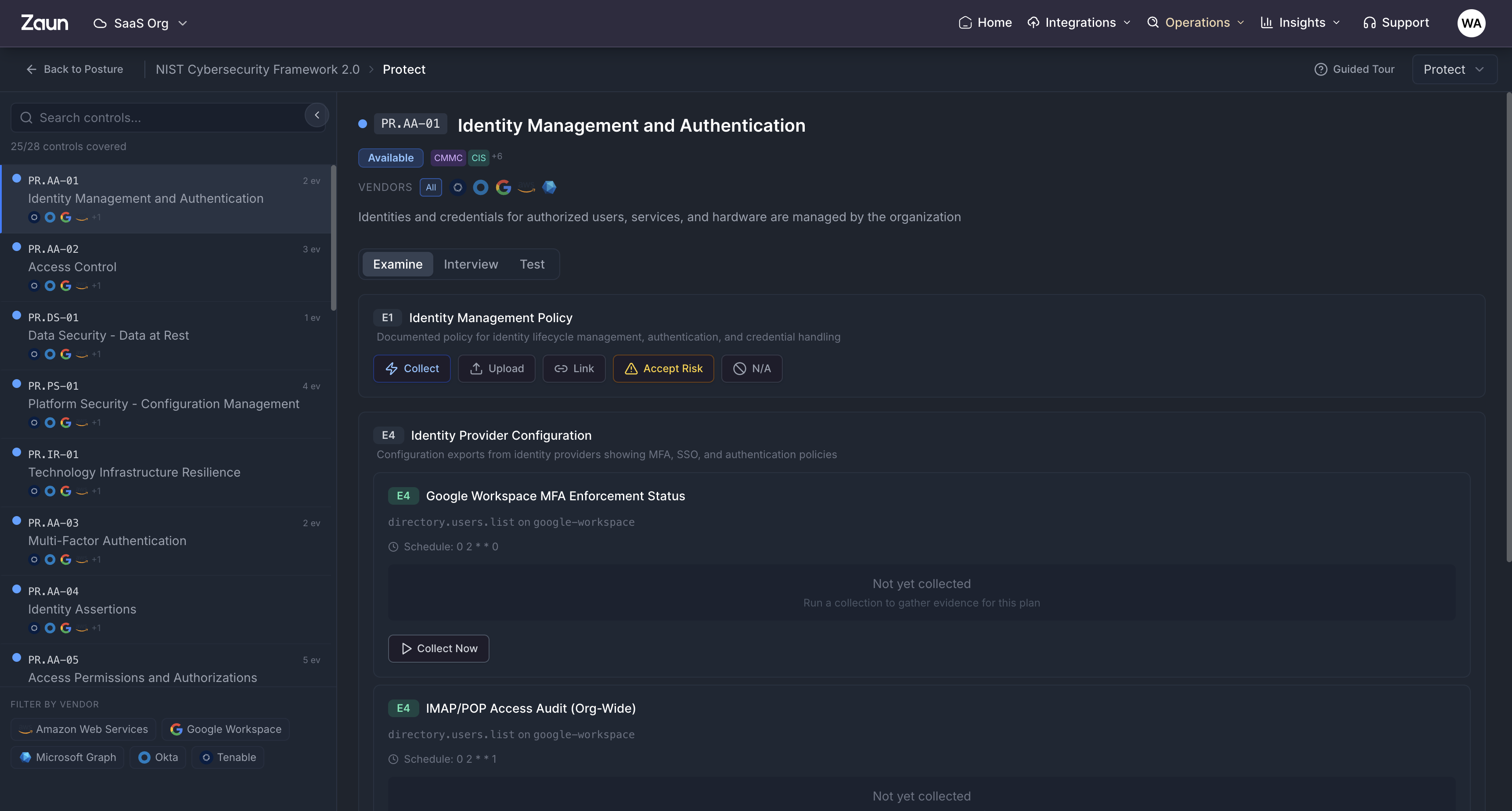
Continuous compliance, evidence-backed.
Map every control to live evidence from your stack. SOC 2, ISO, HIPAA, PCI, CIS, and NIST tracked continuously, with a permanent audit trail you can hand to your auditor without a screenshot scramble.
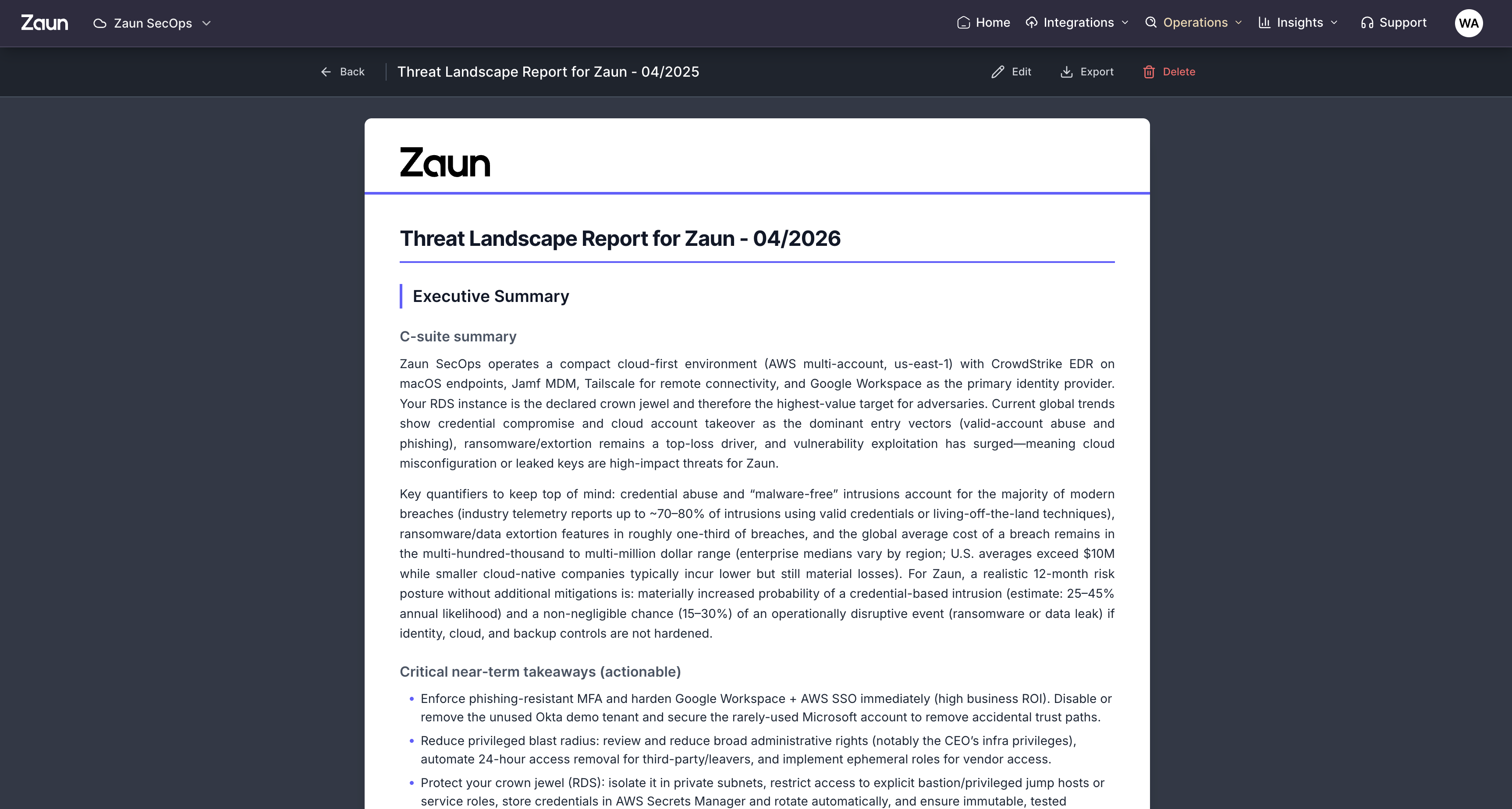
Reports your board actually reads.
Editorial-grade reports that summarize coverage, posture, MTTR, and incidents in plain language. Generated weekly, ready to hand to leadership, the audit committee, or your customers without retouching.
Q2 board readout
May 2026 · Executive summary
SOC 2 evidence pack
Continuous controls report
Weekly coverage
Week 18 · MTTR, incidents, tuning
An engineer who knows your stack, on call.
Every customer gets a named Forward Deployed Engineer. They learn your environment in week one, ship new detections every week, and answer in your Slack/Teams channel directly. No context lost, no tier-1 analysts.